Temporary email services offer convenience but vary wildly in safety. Trust isn’t automatic – it hinges on specific factors like encryption, privacy policies, and provider reputation. Choosing wisely protects you from spam, scams, and data leaks while using these handy tools.
Key Takeaways
- Encryption is non-negotiable: Always choose services using TLS/SSL for email transmission and storage. Unencrypted emails are easily intercepted and read by hackers.
- Privacy policies reveal everything: Scrutinize what the provider does with your data. Avoid services that sell logs, track activity, or retain emails indefinitely – this defeats the purpose of “temporary”.
- Reputation and longevity matter: Established services with positive user reviews and a history of security updates are far more trustworthy than brand-new, obscure platforms.
- Auto-delete features are crucial: True temporary emails vanish automatically after a short period (hours/days). Services keeping emails for weeks or months pose significant privacy risks.
- Beware of suspicious domains and ads: Excessive pop-ups, redirects, or domains mimicking legitimate services (like “gmaill-temp.com”) are major red flags for malware and phishing.
- Understand the limitations: Temporary emails aren’t for sensitive accounts (banking, primary email). Use them only for low-risk sign-ups where you don’t need long-term access.
📑 Table of Contents
- Why Temporary Emails Need Trust Factors (And Why You Should Care)
- What Exactly Are Temporary Email Services? (Beyond the Basics)
- The Critical Risks of Untrustworthy Temporary Emails
- Core Temporary Email Trust Factors: What Makes Them Safe?
- How to Evaluate a Temporary Email Service: Your Step-by-Step Checklist
- Common Pitfalls and When NOT to Use a Temporary Email
- Conclusion: Temporary Emails Are Tools – Use Them Wisely
Why Temporary Emails Need Trust Factors (And Why You Should Care)
Let’s be honest: we’ve all been there. You’re signing up for a free trial, downloading a whitepaper, or joining a forum, and you’re hit with that dreaded email field. You don’t want to hand over your precious personal inbox – who knows what spam or tracking links might follow? Enter the temporary email service. A quick Google search, a few clicks, and boom – you have a disposable address that vanishes after you’re done. Convenience, right? Absolutely. But here’s the catch: not all temporary email services are created equal. In fact, many are downright dangerous. This is where **temporary email trust factors** become absolutely critical.
Think about it. When you use a temporary email, you’re essentially handing over a piece of your digital identity – even if it’s just for a moment – to a third-party service. You’re trusting them to handle that email securely, not snoop on its contents, and crucially, to actually delete it when promised. But how can you know if you *should* trust them? It’s not like they come with a trustworthiness certificate. The reality is, a shoddy temporary email service can be a goldmine for cybercriminals. They might intercept your sign-up confirmation links, harvest data from emails you receive, sell your activity logs to advertisers, or even inject malware into the email viewing interface. Suddenly, that “harmless” disposable address becomes a backdoor into your online life. Understanding **temporary email trust factors** isn’t just technical nitpicking; it’s fundamental to protecting your privacy and security in an increasingly spam-filled world.
The good news? You don’t need to be a cybersecurity expert to spot the difference between a safe temporary email service and a risky one. By focusing on a few key **temporary email trust factors**, you can make informed choices. This isn’t about finding a perfect, bulletproof solution (true anonymity online is incredibly hard), but about significantly reducing your risk. We’ll dive deep into what makes a temporary email service trustworthy, how to evaluate them yourself, and why cutting corners here can have serious consequences. Your inbox – and your peace of mind – deserve this protection.
What Exactly Are Temporary Email Services? (Beyond the Basics)
Before we dissect trust, let’s clarify what we’re talking about. Temporary email services (also known as disposable email addresses or burner emails) provide you with a unique, short-lived email address. You use this address to sign up for services, receive one-time verification codes, or download content without exposing your primary email. The core promise is simple: the address (and often the inbox) disappears after a set period – minutes, hours, or a few days – or once you close the browser tab.
How They Typically Work
The process is usually straightforward. You visit a temporary email website (like Mailinator, Guerrilla Mail, or 10MinuteMail). The site instantly generates a random email address for you (e.g., bluecat42@mailinator.com). This address is now active and ready to receive emails. When someone sends an email to that address, it appears in the web-based inbox on the temporary email site. You can read it, sometimes download attachments, and often forward it to your real email. The magic (or danger) happens after you’re done. A trustworthy service will automatically delete the entire inbox and address after the predetermined time expires. A less trustworthy one might keep logs, retain emails longer, or even reuse the address later.

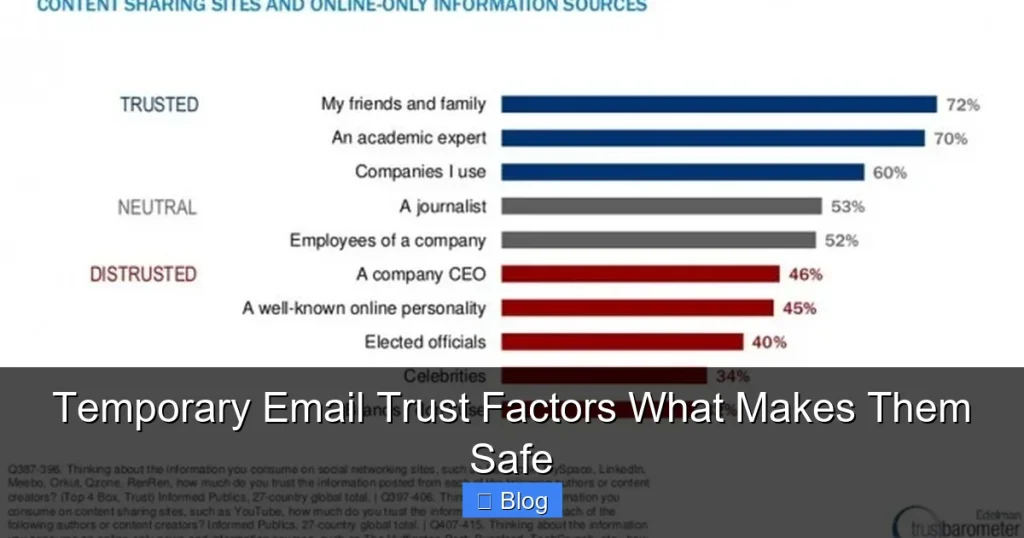
Visual guide about Temporary Email Trust Factors What Makes Them Safe
Image source: i1.sndcdn.com
The Spectrum: From Truly Temporary to Dangerously Permanent
Not all “temporary” services live up to the name. Here’s the critical distinction:
- True Temporary Services: Emails are ephemeral. They exist only for a short, defined window (e.g., 10 minutes, 1 hour, 24 hours). After that, the inbox is wiped clean, and the address becomes unusable. Data is not stored long-term. This is the gold standard for privacy-focused **temporary email trust factors**.
- Pseudo-Temporary Services: These might claim to be temporary but retain emails for days, weeks, or even indefinitely in a database. They might also keep detailed logs of who sent emails and when. This fundamentally undermines the privacy benefit and introduces significant risk. Your “temporary” sign-up could haunt you months later if the service is breached.
- Malicious Services: Some sites masquerade as temporary email providers but are primarily designed to harvest data, serve malware, or facilitate phishing. They might capture every email you receive, including verification links for other accounts, giving attackers access.
Understanding this spectrum is the first step. True safety hinges on a service operating firmly in the “True Temporary” camp, governed by strong **temporary email trust factors**. The convenience is only valuable if the underlying service respects your need for disposability.
The Critical Risks of Untrustworthy Temporary Emails
Using a temporary email service without considering **temporary email trust factors** is like accepting a ride from a stranger without checking their license plate. It might work out fine, but the potential downsides are severe and often overlooked. Let’s break down the real dangers:
Data Harvesting and Privacy Violations
This is the biggest threat. Untrustworthy services often exist primarily to collect data. Every email you receive through their address – sign-up confirmations, download links, even spam sent *to* that address – is potentially logged and stored. They might track:
- Your Activity: Which services you sign up for, what you download, when you access the inbox.
- Email Content: The actual text of messages, including verification codes, password reset links, or personal information shared in sign-up forms.
- IP Address & Device Info: Your location, browser, and device details when you access the inbox.
Why is this bad? This data is incredibly valuable. It can be sold to data brokers, used for targeted (and intrusive) advertising, or even leveraged for identity theft if combined with other leaked information. A service that doesn’t prioritize privacy as a core **temporary email trust factor** turns your attempt at anonymity into a data goldmine for them.
Interception of Sensitive Links and Codes
Think about what you typically use a temporary email for: signing up for a new service. That almost always involves clicking a verification link sent to the temporary address or entering a one-time code (OTP). If the temporary email service is malicious or compromised:
- They can intercept the verification link and click it themselves, potentially gaining access to the account you were trying to create.
- They can read the OTP and use it to take over the account before you do.
- They might modify the email content, replacing legitimate links with phishing links designed to steal your credentials when you click.
This transforms your temporary email from a privacy tool into an attack vector, directly compromising other accounts. Trust factors like end-to-end encryption (though rare in temp email) and secure handling are vital here.
Malware Distribution and Phishing
Shady temporary email sites are notorious for aggressive advertising and pop-ups. These aren’t just annoying; they’re dangerous:
- Malicious Ads: Pop-ups might mimic system alerts (“Your computer is infected!”) or fake download buttons, tricking you into installing malware or visiting phishing sites.
- Email Injection: Some services might inject malicious scripts or links directly into the emails you view within their interface, compromising your browser session.
- Phishing Mimicry: The site itself might look like a legitimate service (e.g., “Gmail Temp”) to steal your credentials if you mistakenly enter your real email password.
A lack of ad quality control and security practices are major red flags against **temporary email trust factors**. A trustworthy service minimizes intrusive ads and rigorously scans for malicious content.
Account Takeover and Reputation Damage
If a temporary email service is breached (and many low-quality ones are), all the data they’ve hoarded – your sign-up history, email contents, IP logs – becomes public. Attackers can use this to:
- Target You Specifically: Knowing you signed up for Service X, they can craft highly convincing phishing emails impersonating Service X.
- Correlate Identities: Linking your temporary email activity to your real identity (if any data was leaked elsewhere), building a detailed profile.
- Abuse the Address: If the address isn’t truly temporary and gets reused, spammers or scammers might start using it, potentially getting it blacklisted and affecting your ability to use *real* email services.
The fallout from using an untrustworthy service can extend far beyond the initial sign-up, impacting your online reputation and security for a long time. This underscores why evaluating **temporary email trust factors** is an investment in long-term safety.
Core Temporary Email Trust Factors: What Makes Them Safe?
Now that we’ve seen the risks, let’s focus on the solution. What actually makes a temporary email service trustworthy? It boils down to several concrete **temporary email trust factors**. Think of these as your checklist when evaluating any provider:
1. Robust Encryption: The First Line of Defense
This is non-negotiable. Encryption protects your email data both while it’s traveling across the internet (in transit) and while it’s sitting on the service’s servers (at rest).
- TLS/SSL for Transmission: When you send an email *to* the temporary address or access the inbox *from* the service, the connection must use TLS (Transport Layer Security), the same encryption securing your online banking. Look for
https://in the URL and a padlock icon in your browser. Without this, hackers on the same public Wi-Fi could easily intercept your emails and verification links. This is a fundamental **temporary email trust factor**. - Encryption at Rest (Ideal but Rare): Truly secure services encrypt emails stored on their servers. Even if their database is hacked, your email content remains unreadable without the decryption key. While less common in free temp email services due to cost, it’s a strong indicator of commitment to security. Ask: “Are emails encrypted on your servers?”
Practical Tip: Always check for https:// and the padlock *before* using any temporary email site. If it’s just http://, close the tab immediately – your data is exposed.
2. Ironclad Privacy Policy & Data Handling Practices
This is where many services fail spectacularly. Your privacy policy isn’t just legal jargon; it’s a promise about how your data is treated. Scrutinize it for these **temporary email trust factors**:
- No Long-Term Logging: The policy should explicitly state that email content, sender addresses, and recipient addresses are not stored after the inbox expires (e.g., “Emails are deleted permanently after 60 minutes”). Avoid policies saying “logs may be retained for security purposes” without a very short, defined timeframe (hours, not days/weeks).
- No Data Selling/Sharing: There should be a clear statement that user data (including email content and activity logs) is never sold, shared, or rented to third parties for advertising or data brokering. Beware of vague language like “we may share data with partners.”
- Minimal Metadata Collection: While some metadata (like timestamp of receipt) might be necessary for function, the policy should state that only the absolute minimum data required for the service to operate is collected, and it’s deleted promptly.
- Transparency About Exceptions: Reputable services will disclose if they are legally compelled to retain data (e.g., by court order) and how they handle such requests.
Practical Tip: Don’t skip the privacy policy! Look for services that have a clear, concise, and user-friendly privacy page (not buried in legalese). If it’s impossible to find or deliberately vague, that’s a massive red flag against **temporary email trust factors**.
3. Reputation, Longevity, and Transparency
Trust is built over time. A service’s history and how openly they operate are vital **temporary email trust factors**:
- Established Track Record: How long has the service been operating? Services like Mailinator (founded 2005) or Guerrilla Mail (founded 2006) have weathered the test of time, indicating reliability and user trust. New services popping up overnight are far riskier.
- Positive User Reviews & Community Trust: Search for independent reviews on tech forums (Reddit’s r/privacy, r/techsupport), Trustpilot, or privacy blogs. Look for consistent praise regarding security, uptime, and adherence to privacy promises. Be wary of services with numerous complaints about data leaks, excessive ads, or broken functionality.
- Transparency About Ownership & Operations: Who runs the service? A legitimate provider will have clear “About Us” or “Contact” pages with identifiable information (even if pseudonymous, there should be accountability). Anonymous services operating from obscure locations are high-risk. Do they explain their security measures?
- Open Source (Bonus): Some services (like TempMail’s open-source versions) publish their code for public audit. While not essential for end-users, it demonstrates a commitment to transparency and allows security experts to verify claims.
Practical Tip: Do a quick Google search for “[Service Name] review privacy” or “[Service Name] scam”. See what the broader community says. Longevity and positive sentiment are strong indicators of trustworthiness.
4. True Ephemerality: Auto-Delete is King
This is the very definition of “temporary.” A core **temporary email trust factor** is how reliably and quickly emails vanish:
- Short, Defined Expiry: Emails should automatically delete after a short, predictable period – typically 10 minutes, 1 hour, 24 hours, or when the browser session ends. Avoid services that keep emails for “up to 30 days” or require manual deletion (which users often forget).
- No Persistent Inboxes: The inbox should not persist across browser sessions or devices unless you explicitly create an account (which many pure temp services avoid for privacy). Closing the tab should effectively end the session.
- Clear Expiry Indicators: The service should clearly show how long the inbox will remain active (e.g., “This inbox expires in 59 minutes”).
Practical Tip: Test it! Sign up for a low-risk service (like a newsletter you don’t care about) using the temp email. Check if the email arrives. Then, wait the stated expiry time and try to access the inbox again. Does it truly disappear? If emails linger, the service isn’t truly temporary.
5. Clean Interface & Minimal Malicious Ads
While not directly about data security, the user experience reveals much about a provider’s ethics and operational security – key aspects of **temporary email trust factors**:
- Controlled Advertising: Reputable services use non-intrusive, contextual ads. They rigorously vet ad networks to prevent malware-laden pop-ups, fake download buttons, or scareware (“VIRUS DETECTED!”). Excessive, flashing, or deceptive ads are a huge red flag.
- No Forced Redirects: You shouldn’t be bombarded with multiple redirects to other sites just to access your inbox or read an email. This is a common tactic for ad fraud and malware distribution.
- Clean, Functional Design: While aesthetics aren’t everything, a professional, well-maintained interface suggests the operators care about quality and security, not just quick ad revenue. Clunky, broken sites are often neglected and insecure.
Practical Tip: If the site feels sketchy, loads slowly due to ads, or tries to trick you with fake “Download” buttons, leave immediately. Your browser’s security is at risk, and the service likely has poor operational hygiene.
How to Evaluate a Temporary Email Service: Your Step-by-Step Checklist
Armed with the knowledge of key **temporary email trust factors**, here’s exactly how to vet a service before you use it:
Step 1: The Initial Scan (5 Seconds)
- Check the URL: Is it
https://with a padlock? If not, close the tab now. No encryption = no trust. - Scan for Red Flags: Are there overwhelming pop-ups, fake virus alerts, or “CLICK HERE TO CONTINUE” buttons? Is the domain name suspiciously similar to a major provider (e.g., “gmaill-temp.com”)? If yes, leave immediately.
Step 2: Dig into the Privacy Policy (2-3 Minutes)
- Find the Policy: Look for links in the footer (“Privacy,” “Terms,” “About”). If it’s hard to find, that’s bad.
- Key Questions:
- How long are emails stored? (Must be short: minutes/hours, not days/weeks).
- Is email content logged or stored long-term? (Should be “No”).
- Is user data (activity, IP) sold or shared? (Should be “No”).
- What data is collected minimally? (Should be very little).
- Verdict: If the policy is vague, says data is kept “for security,” or mentions sharing/selling, do not use this service. Move on.
Step 3: Research Reputation (3-5 Minutes)
- Google Search: “[Service Name] review privacy”, “[Service Name] scam”, “[Service Name] data leak”.
- Check Forums: Search Reddit (r/privacy, r/techsupport) for mentions. What do experienced users say?
- Look for Longevity: When was it founded? (Check “About Us” or Wikipedia). Older = generally better.
- Verdict: If searches reveal consistent complaints about privacy, malware, or broken promises, avoid it. Positive, long-standing reviews are a green light.
Step 4: Test the Ephemerality (Optional but Recommended)
- Sign Up for Something Trivial: Use the temp email to subscribe to a low-risk newsletter or download a free guide.
- Check Expiry: Note the stated expiry time. Wait that time plus a buffer (e.g., if 1 hour, wait 90 mins).
- Try to Access: Go back to the service. Can you still see the email? If yes, the service isn’t truly temporary – consider it untrustworthy.
Step 5: Assess the User Experience
- Ads: Are they reasonable and non-malicious? Or are you fighting pop-ups and fake downloads?
- Functionality: Does the inbox load quickly? Can you read emails without constant redirects?
- Verdict: A clean, functional experience with minimal intrusive ads supports trust. A clunky, ad-infested mess undermines it.
Trusted Service Examples (Illustrative – Always Verify!): Based on historical reputation and stated practices (do your own check!):
- Mailinator: Very old (2005), public inbox model (emails visible to anyone knowing the address), strong privacy policy stating emails are deleted after ~1 hour, minimal logging. *Note: Public inbox means anyone can read emails sent to common addresses like “test@mailinator.com” – use a unique random address.*
- Guerrilla Mail: Established (2006), offers temporary addresses with auto-delete (1 hour default), clear privacy policy emphasizing no long-term storage, generally clean interface.
- 10MinuteMail: Simple, focuses on the 10-minute expiry, straightforward privacy policy stating emails are deleted after expiry.
Remember: Reputation can change. Always apply the checklist, even to familiar names. **Temporary email trust factors** require ongoing vigilance.
Common Pitfalls and When NOT to Use a Temporary Email
Even with trustworthy services, misusing temporary emails creates risks. Avoid these critical mistakes:
Pitfall 1: Using Them for Sensitive Accounts
This is the cardinal sin. Never use a temporary email for:
- Your primary email account recovery
- Banking, investment, or cryptocurrency platforms
- Government services (taxes, benefits)
- Healthcare portals
- Employer-related accounts
Why? If you lose access to the temporary email (it expires, the service shuts down), you lose access to the sensitive account forever. Recovery options often require the original email. Trust factors don’t mitigate this fundamental limitation – the address *is* temporary by design. Use a dedicated, secure, long-term email for anything important.
Pitfall 2: Ignoring the “From” Address
When you receive an email in your temporary inbox, always check the actual sender’s email address, not just the display name. Scammers often spoof legitimate companies (e.g., “Amazon Security” but sent from amaz0n-support@badsite.ru). A trustworthy temp email service won’t prevent phishing; it’s your job to verify the sender. Don’t click links or download attachments from unexpected senders, even in a temp inbox.
Pitfall 3: Assuming Complete Anonymity
Temporary emails hide your *real* email address from the service you’re signing up for, but they don’t make you anonymous online. The temporary email service itself sees your IP address when you access the inbox. If that service logs IPs (and many do, even reputable ones, for basic function), and if they are compromised or subpoenaed, that link exists. True anonymity requires more advanced tools (like Tor combined with careful practices). **Temporary email trust factors** protect you from the *sign-up service* and *some* tracking, but not from the temp email provider itself or sophisticated adversaries.
Pitfall 4: Relying on Them for Important Communications
Temporary emails are for one-offs. Don’t use them for:
- Signing up for services where you expect ongoing important communications (e.g., flight confirmations, subscription renewals).
- Providing an email for customer support – you likely won’t be able to access replies later.
- Anything where you might need to prove ownership or history later.
If you need to keep access, use a dedicated alias service (like SimpleLogin or Firefox Relay) that forwards to your real inbox but still hides it, or create a unique long-term email just for that service.
Pitfall 5: Overlooking Browser Security
Using a temp email on a compromised device (malware, keylogger) negates all trust factors. Ensure your device is secure:
- Keep your OS and browser updated.
- Use a reputable antivirus/anti-malware solution.
- Avoid using temp emails on public computers or unsecured Wi-Fi without a VPN.
Your local security is the foundation; **temporary email trust factors** build on top of that.
Conclusion: Temporary Emails Are Tools – Use Them Wisely
Temporary email services are incredibly useful tools in our digital arsenal. They offer a vital shield against spam, reduce the footprint of your primary email, and provide a layer of privacy for low-risk online interactions. But like any tool, their safety and effectiveness depend entirely on how you use them and, crucially, which tool you choose. The convenience means nothing if the service itself becomes a vulnerability.
We’ve explored the essential **temporary email trust factors** that separate the secure from the shady: robust encryption (especially TLS for transmission), a privacy policy that truly respects ephemerality and refuses data exploitation, a solid reputation built on longevity and transparency, the ironclad promise of auto-deletion, and a clean, ad-safe user experience. These aren’t optional extras; they are the bedrock of trust. Ignoring them turns a privacy tool into a potential liability, exposing you to data harvesting, account takeover, malware, and long-term tracking.
The key takeaway is vigilance. Don’t just grab the first temporary email link you find. Take the few extra minutes to apply the checklist: verify HTTPS, read the privacy policy (really read it!), check the reputation, and understand the expiry. Remember their limitations – never use them for sensitive accounts or expecting long-term access. Pair this careful selection with smart usage habits: verify sender addresses, avoid clicking suspicious links even in temp inboxes, and maintain good overall device security.
By prioritizing **temporary email trust factors**, you transform these disposable addresses from a potential risk into a reliable, safe component of your online privacy strategy. You gain the freedom to explore, sign up, and download without constantly worrying about polluting your main inbox or compromising your security. In a world overflowing with data collectors and spammers, that controlled, temporary anonymity is not just convenient – it’s increasingly essential. Choose wisely, use responsibly, and enjoy the peace of mind that comes from knowing your temporary email is truly temporary and trustworthy.
Frequently Asked Questions
Are temporary email services legal?
Yes, using temporary email services is completely legal in most jurisdictions. They are legitimate tools for privacy and spam reduction. However, using them for illegal activities (like fraud or harassment) is obviously unlawful, regardless of the email type.
Can I receive attachments with a temporary email?
Most reputable temporary email services allow you to receive and download attachments, just like a regular email. However, be extremely cautious: attachments are a common malware delivery method. Only open attachments from trusted senders, and ensure your device has updated security software. Some services may block certain file types for safety.
Do temporary email services prevent spam completely?
No, they significantly reduce spam sent *to your primary email address* for the specific sign-ups you use them for. However, spammers might still find the temporary address itself (e.g., if it’s a common name on a public service like Mailinator) and send spam directly to it. The key benefit is keeping your main inbox clean; the temp inbox will still get spam, but it vanishes automatically.
What happens if the temporary email service shuts down?
This is why auto-delete is crucial. With a trustworthy service adhering to strong **temporary email trust factors**, your emails are already deleted after the short expiry period (e.g., 1 hour). Even if the entire service disappears later, there should be no stored emails or logs of yours to be lost or exposed. Avoid services that retain data long-term, as a shutdown could mean your historical sign-up data is dumped online.
Can temporary emails be traced back to me?
The temporary email service itself typically sees your IP address when you access the inbox. A trustworthy service with strong privacy practices (a key **temporary email trust factor**) will not log this IP long-term or link it to your activity beyond the immediate session. However, if the service is compromised, retains logs, or is legally compelled, that link *could* potentially be made. They hide your identity from the *sign-up service*, but not necessarily from the temp email provider itself if they mishandle data.
Are paid temporary email services more trustworthy?
Not necessarily. While some paid services might offer enhanced features (longer expiry, custom domains, better support), trust depends on the specific **temporary email trust factors** (privacy policy, encryption, reputation), not the price. Many excellent free services operate with strong ethics. Conversely, some paid services might still have poor privacy practices. Always evaluate based on the checklist, regardless of cost. Free services often rely on non-intrusive ads; be wary if a paid service still has excessive malicious ads.