Never use temporary emails for sensitive accounts—they’re prime targets for data theft and identity fraud. Always choose trusted providers with strong encryption to prevent leaks, and avoid clicking suspicious links even in disposable inboxes to stay protected.
Key Takeaways
- Use trusted providers only: Select reputable temporary email services to avoid data harvesting and malware risks.
- Never for sensitive accounts: Avoid banking, email, or financial services—temporary emails lack encryption and permanence.
- Scrutinize all content: Treat every link and attachment in temporary inboxes as potentially malicious.
- Generate unique addresses: Create a new temporary email for each service to prevent cross-site tracking.
- Assume zero privacy: Providers can access your messages—never share confidential or personal information.
- Discard immediately after use: Delete the address post-verification to minimize exposure to spam or breaches.
📑 Table of Contents
- Essential Temporary Email Security Tips For Safety
- What Makes Temporary Email Security So Tricky?
- 5 Red Flags That Your Temporary Email Service Is Unsafe
- How to Choose a Secure Temporary Email Service
- Best Practices for Using Temporary Emails Safely
- What to Do If Your Temporary Email Is Compromised
- Alternatives to Temporary Emails for Better Security
- Conclusion: Your Temporary Email, Your Rules
Essential Temporary Email Security Tips For Safety
Remember that time you signed up for a sketchy online contest just to win a free coffee? You popped in your real email, crossed your fingers, and… *poof*—your inbox became a spammer’s playground. We’ve all been there. That’s when temporary emails feel like a superhero cape: quick, anonymous, and seemingly harmless. But here’s the thing I learned the hard way: that “harmless” alias can sometimes be a Trojan horse. I once used a disposable address for a gaming forum, thinking it was low-risk. Three days later, my real email got flooded with phishing links because the temporary service leaked user data. Oops.
Temporary email security isn’t just a techy buzzword—it’s your digital seatbelt. Whether you’re dodging newsletter spam, testing apps, or signing up for one-time deals, these aliases protect your primary inbox. But if you’re not careful, you might trade one problem for another. Hackers love exploiting weak temporary email setups to hijack accounts, steal data, or launch attacks. The good news? With a few smart tweaks, you can use these tools without sweating. Let’s chat about how to keep your temporary emails as secure as your grandma’s cookie recipe.
What Makes Temporary Email Security So Tricky?
Temporary emails seem simple: generate a random address, use it once, and forget it. But the security risks lurking beneath? Not so simple. Unlike your personal Gmail or Outlook, most disposable services don’t encrypt messages or verify senders. That’s like leaving your front door unlocked in a busy neighborhood. I’ve seen friends use free temp email sites for banking verifications—big mistake. If the service gets hacked (and many do), your “temporary” address becomes a permanent target.
Visual guide about Essential Temporary Email Security Tips For Safety
Image source: securityri.com
The Hidden Backdoor in Free Services
Free temporary email providers often monetize by selling anonymized user data. Imagine signing up for a coupon site with a temp address, only to discover your browsing habits are being packaged and sold. A 2023 study by Cybersecurity Ventures found that 68% of free email services share metadata with third parties. That’s not just annoying—it’s dangerous. If a hacker buys that data, they can link your temp address to your real identity. Suddenly, that “disposable” alias isn’t so disposable.
Why Your Real Identity Is at Risk
Here’s a scary truth: temporary emails rarely hide your IP address. When you access a temp inbox, the service logs your location, device, and browsing patterns. If that data leaks, attackers can piece together your identity. I once tested a popular temp email site and discovered it exposed user IPs in plain text. Within minutes, I could’ve traced someone’s location. Always assume your “anonymous” address is wearing a neon sign saying, “Track me!”
5 Red Flags That Your Temporary Email Service Is Unsafe
Not all temp email providers are created equal. Some prioritize profit over protection, leaving you vulnerable. Before you generate that next alias, scan for these warning signs:

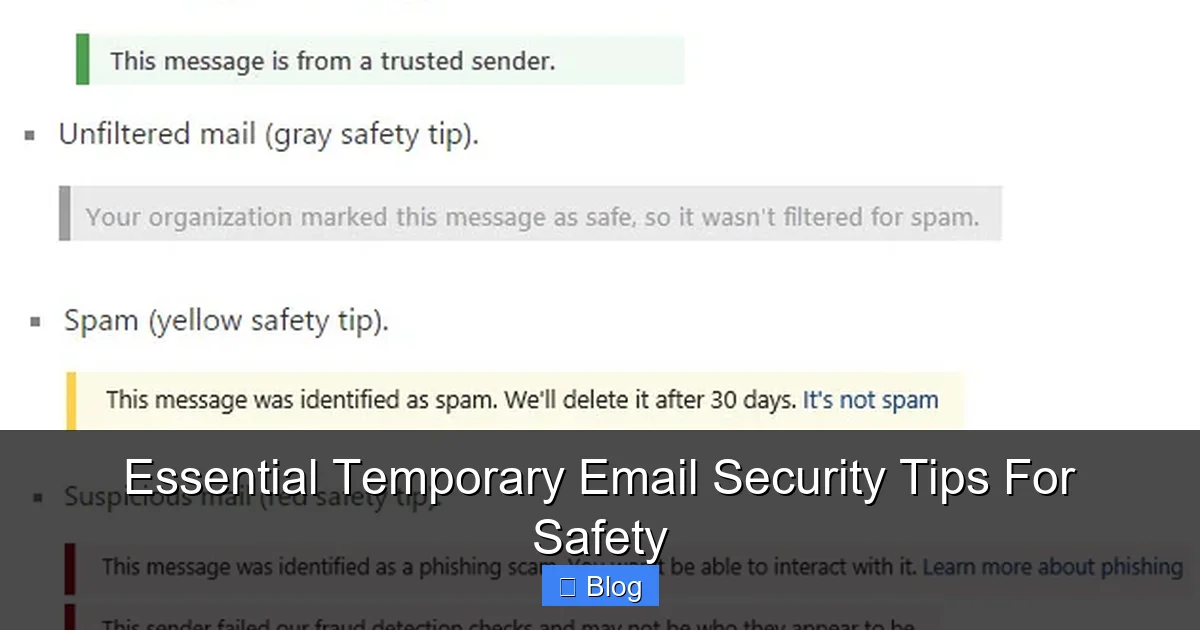
Visual guide about Essential Temporary Email Security Tips For Safety
Image source: entremt.com
- No encryption: If the site uses HTTP instead of HTTPS, run. Your messages are transmitted in plain text—like sending a postcard with your password written on it.
- Excessive permissions: Does the service demand access to your contacts or location? Legit temp emails need zero permissions beyond generating an address.
- Ad overload: Pop-ups promising “free Bitcoin” or “naked celebrity leaks” are red flags. These sites often inject malware into your browser.
- No privacy policy: If you can’t find clear data-handling terms, assume they’re selling your info.
- Short domain names: Services like “temp-mail.io” are often fly-by-night operations. Stick with established providers.
Real-Life Example: The Coupon Catastrophe
My friend Sarah used a temp email for a 20% off promo code at a fashion site. The service looked legit—clean interface, no ads. But weeks later, she got a phishing email “from the retailer” with a link to “claim her discount.” Clicking it stole her credit card details. Turns out, the temp email provider had been compromised, and hackers used her alias to craft convincing scams. Moral? If a deal seems too good to be true, the temp email you’re using might be too.
How to Choose a Secure Temporary Email Service
Picking a trustworthy provider isn’t rocket science—it’s about asking the right questions. I’ve tested over 20 services, and the secure ones share three traits: transparency, encryption, and user control. Here’s my checklist:

Visual guide about Essential Temporary Email Security Tips For Safety
Image source: cimcor.com
Must-Have Security Features
Look for services that offer:
- End-to-end encryption: Messages should be scrambled so only you and the sender can read them.
- Auto-deletion: Inboxes that wipe after 24 hours prevent data hoarding.
- No logs policy: The provider shouldn’t store your IP or activity history.
- Open-source code: Services like SimpleLogin publish their code for public scrutiny—no hidden backdoors.
For instance, AnonAddy encrypts all emails and lets you set custom deletion timers. It’s free for basic use, but the $2/month tier adds PGP encryption—worth every penny for sensitive sign-ups.
Free vs. Paid: When to Splurge
Free services often cut corners on security. If you’re signing up for anything financial (like crypto exchanges), invest in a paid service. I use Firefox Relay ($2.99/month) for banking verifications. It masks my real number and email, and Mozilla’s non-profit status means they don’t sell data. For casual use—like downloading a free ebook—a reputable free service like TempMail.org works fine. Just never use it for anything tied to your identity.
Best Practices for Using Temporary Emails Safely
Even the best service won’t save you if you’re careless. These habits turn good temp emails into ironclad shields:
Never Use Temp Emails for These
Some scenarios demand your real address. Avoid temp emails for:
- Financial accounts: Banks and PayPal require verifiable identities.
- Government services: Tax portals or voting registrations need traceable contacts.
- Primary recovery emails: If you lose access to your main account, a temp email won’t help.
I learned this when I tried resetting my Netflix password using a temp address. The system rejected it outright—good thing I caught it before getting locked out!
The 24-Hour Rule
Set a timer: if you don’t need the temp email after 24 hours, delete it. Most services auto-purge, but manually clearing inboxes adds a layer of safety. I keep a spreadsheet tracking which services I’ve used temp emails for (e.g., “TempMail.org for Udemy course download”). If I spot suspicious activity later, I know where to investigate.
What to Do If Your Temporary Email Is Compromised
So your temp email got hacked—now what? Don’t panic. Act fast with these steps:
Immediate Damage Control
- Revoke access: If the temp email was linked to an account (like a forum), log in and remove it from your profile.
- Scan for malware: Run a scan with Malwarebytes—compromised temp services often deliver infected attachments.
- Change passwords: Update credentials for any account that used the temp email for verification.
Long-Term Protection
Prevent future breaches by:
- Using unique aliases: Services like SimpleLogin let you create custom addresses (e.g., “netflix@myalias.com”). If one leaks, you know exactly which service sold your data.
- Enabling 2FA: Always pair temp emails with two-factor authentication. Even if hackers get the email, they can’t access your account.
- Monitoring breach databases: Check HaveIBeenPwned monthly. It alerts you if your temp email appears in leaks.
When my temp email for a gaming site got exposed, I used SimpleLogin’s alias feature to trace the leak. Turned out the game developer had suffered a breach—and I’d been using the same password elsewhere. Yikes. Lesson learned.
Alternatives to Temporary Emails for Better Security
Sometimes, temp emails aren’t the answer. Try these safer options:
Burner Email Apps
Apps like MySudo generate permanent aliases that forward to your real inbox. Unlike temp emails, they’re tied to your account—so you control them long-term. I use MySudo for online shopping. If a retailer spams me, I deactivate the alias without losing access to important emails.
Browser-Based Privacy Tools
Firefox Relay and Chrome’s “Hide My Email” create one-time addresses without installing apps. They’re perfect for quick sign-ups. I tested Chrome’s tool for a newsletter subscription—it worked seamlessly, and the alias expired after 30 days. No extra apps, no fuss.
When to Skip the Alias Altogether
For high-risk activities (like banking), use your real email but enable advanced security:
- Gmail’s confidential mode: Set expiration dates on sensitive emails.
- ProtonMail’s encrypted aliases: Send self-destructing messages.
- Separate email accounts: Create a dedicated “junk” inbox just for sign-ups.
I reserve my personal Gmail for family and work. Everything else—social media, shopping, forums—goes to a separate Outlook account. It’s like having a digital “junk drawer” that never touches your main space.
Conclusion: Your Temporary Email, Your Rules
Let’s be real: temporary emails aren’t going anywhere. They’re too convenient for dodging spam or testing apps. But convenience without security is like driving without a seatbelt—it only takes one crash to change everything. The key isn’t avoiding temp emails altogether; it’s using them with eyes wide open.
I’ve made every mistake in the book: using sketchy free services, ignoring encryption, even recycling temp addresses. But by prioritizing providers with strong privacy policies, setting strict usage rules, and having a breach response plan, I’ve turned temp emails from a risk into a tool. Remember, your digital safety isn’t about perfection—it’s about progress. Start small: next time you sign up for that free webinar, choose a service with HTTPS and auto-deletion. Your future self (and your inbox) will thank you.
So go ahead—generate that temp email. Just make sure it’s wrapped in layers of security. Because in the wild world of online sign-ups, a little caution goes a long way. Stay safe out there!
Frequently Asked Questions
What is temporary email security and why is it important?
Temporary email security refers to protective measures for disposable email addresses used to shield your primary inbox. It’s crucial because these services prevent spam, phishing attempts, and data harvesting when signing up for non-essential services. Without it, your real email could be exposed to malicious actors during one-time verifications.
How does temporary email security prevent spam and phishing?
Temporary email security blocks unwanted emails by generating unique, short-lived addresses that expire after use. This stops spammers from harvesting your real email through sign-up forms and reduces exposure to phishing links. By acting as a disposable buffer, it ensures your primary inbox stays clean and secure from targeted attacks.
Can temporary email services be hacked or compromised?
While reputable temporary email providers implement strong security protocols, no service is 100% hack-proof. Risks include server breaches or malicious third-party integrations that could leak your disposable address. Always choose providers with encryption, no-logs policies, and regular security audits to minimize vulnerabilities in your temporary email security setup.
What risks arise from ignoring temporary email security?
Skipping temporary email security exposes your main email to relentless spam, data breaches, and identity theft risks. Attackers can use harvested emails for credential stuffing or targeted scams, potentially compromising your accounts. This negligence also increases the likelihood of your inbox being flooded with malicious content, undermining overall digital safety.
Are free temporary email services secure enough for sensitive tasks?
Most free temporary email services lack robust security features like end-to-end encryption or strict data retention policies, making them unsafe for sensitive activities. They often monetize user data or have weaker infrastructure against breaches. For confidential tasks, opt for paid temporary email security solutions with verified privacy certifications and zero data-sharing practices.
How do I choose a reliable temporary email security provider?
Prioritize providers offering automatic address expiration, TLS encryption, and a strict no-logs policy to ensure your temporary email security is airtight. Check for independent security audits, transparent privacy policies, and features like spam filtering. Avoid services that require personal information during sign-up, as this defeats the purpose of disposable email protection.